Administrator can limit the use of computer and network resource on agent computer by setting policies to control staffs’ and childs' computer usage and improve productivity.
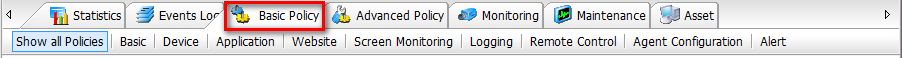
Basic policies |
|
 |
|
| Basic Policy | Assgin monitored users operation privileges on Control Panel, Computer Managements, System, Network, IP/Mac, ActiveX and other operations, protect the safety of monitored computers. [View details...] |
| Device Policy | Define what devices can be used or not. [View details...] |
| Application Policy | Define what applications can be used or not. [View details...] |
| Web Policy | Define what websites can be visited or not. [View details...] |
| Screen Snapshot Policy | Decide whether to record screen snapshot and if enabled, set recording interval. [View details...] |
| Logging Policy | Check what logs you need to record. By default, all kinds of logs will be recorded. [View details...] |
| Remote Control Policy | Decide whether remote computers can be controlled and if enabled, set remote controlling method. [View details...] |
| Agent Configuration | Commonly used agent control functions. [View details...] |
| Alert Policy | Set real-time alerts when software change, hardware change or system settings change happens so that IT manager can find any changes and take actions immdediately. [View details...] |
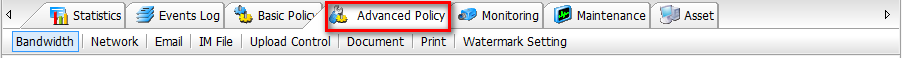
Advanced policies |
|
 |
|
| Bandwidth Policy | Control bandwidth including upload and download speed of monitored computers. [View details...] |
| Network Policy | Control communication between agent computer and any invalid computers, ensure network safety. [View details...] |
| Email Policy | Control email sending and receiving by sender, receiver, address, attatchment, etc. and prevent email spams. [View details...] |
| IM File Policy | Control file transfer via instant messengers and back up transferred files. [View details...] |
| Upload Control Policy | Control the network upload behavior by way of HTTP or FTP, including sending webmail, uploading images, forum posting and FTP upload, etc. [View details...] |
| Document Policy | Define document operation privileges and back up documents if necessary. [View details...] |
| Print Policy | Control the usage of various printers. [View details...] |
| Watermark Setting Policy | Add Image/Text watermark to documents printing out. [View details...] |
All the policies have some properties in common.
Properties | Value |
| Name | Set the policy name. SurveilStar will automatically add a policy name when a policy is created. You can customize the name later. We recommend you use a brief description of the policy as the policy name. |
| Time | Specify time range that the policy will take effect. You can select time types which are set in 【Categories > Time Types】. If not suitable time type available, click |
| Action | Select execution action when all the conditions of the policy are met. There are some actions can be selected to be executed: Allow, Block, Ingore and No Action. Allow: Allow to perform an operation. If the policy mode the operation matches is Allow, then the operation is allowed and the coming policies won't be judged. Block: Block a certain operation. If the policy mode the operation matches is Block, then the operation is blocked and the coming policies won't be judged. Ingore: The operation won't be allowed nor blocked, but it can trigger events such as warning or alert. Once the current No Action policy completed, system continues to search the following related policies. For example, the first policy is setting all *.doc with Ignore mode and alert; the second policy is prohibiting copy *.doc files. Whenaccessing the doc files, the first policy matched (i.e. alert popup) and then the following second policy will also be matched too, and determine the accessing action is copy or not. If it is copy, action prohibited. No Action: The operation won't be allowed nor blocked, but it can trigger events such as warning or alert. Once the current Ignore policy completed, the following policies will not be executed. For example, the first policy is setting the mode for USB device as Inaction and the second policy is prohibiting USB device. When USB device is plugged in, the first policy matched. Since the modeis Inaction, it will not be blocked but the following second policy will not be matched. |
| Alert & Alert Severity | Enable or disable alert to SurveilStar Console and Server. When a user's operation matches a certain policy, agent computer will send alert information to SurveilStar server, and alert will also pop up in SurveilStar console to remind IT manager or supervisor. Meanwhile, this alert will be also recorded in policy logs. IT manager can use menu 【Tools > Options > Console Settings > Real-time Alert > Popup alert bubble】 to enable or disable alert popup, use menu 【Tools > Alert】 to review real-time alerts. Choose alert severity if <Alert> is enabled. Low, High and Critical are available. |
| Warning & Warning Message | Enable or disable warning message to show on agent PC. Click |
| Lock Computer | Check this option to lock agent PC if the policy matched. Then user can't do anything on this client computer. IT manager can unlock the PC via menu 【Control > Unlock】 on SurveilStar Console. |
| Expiring Time | Set effective date of the policies. By default, it is set to <Never Expire>. Click |
| Take effect while offline | The agent computer will be treated as offline status when the agent PC can't communicate with the server over 3 minutes due to shutdown, network problem, etc. Check this option if you want the policy to be effective only when the computers are offline. Usually selected when agnet user is for business trip or under network failure conditions. |
Properties | Value |
 |
|
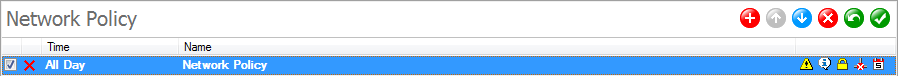
| New: Create a new policy. | |
| Up: Move up the selected policy. | |
| Down: Move down the selected policy. | |
| Delete: Delete the selected policy. | |
| Undo: Cancel the newly created policy or cancel policy modification. | |
| Save: Save all new added or modified settings. | |
| The policy execution action is set to <Allow>. | |
| The policy execution action is set to <Block>. | |
| The policy execution action is set to <Ignore>. | |
| The policy execution action is set to <No Action>. | |
| <Alert> is enabled. | |
| <Warning> is enabled. | |
| <Lock Computer> is enabled. | |
| <Take effect while offline> is enabled. The policy would only be effective only when the computers are offline. | |
| <Expiration Time> is enabled. The policy would be expired and invaild specified date. | |
Usually there will be multiple policies applied to a certain computer or a group and there may be policy conflict problems. Thus there will be a policy priority. Policy adopted mechanism is similar to Firewall, each goal can be combined from a number of policies and then matched in accordance with their relationships. At the same time, different computers (group) or users (group) inherit their parents’ policies.
IT manager or supervisor can create user policy, computer policy, group policy and whole network policy. Please note that: User policy has higher priority than computer policy; self policy has higher priority than group priority; policy on top has higher priority than the policy below. When a policy found in higher priority, it will be executed and the policies in lower priority will be ignored. The priority of the policies from high to low is as below:
User Policy > User Group Policy > Computer Policy > Computer Group Policy > The Whole Network Policy
When a policy is inherited from a parent object, it will be displayed in light green background and can't be modified in child object. If the policy can be customized by entering words, then you can use wild-card(*). Multiple strings can be entered and you should use half-size "," or ";" to separate. Up to 3 wild-card(*) is allowed.
Select a computer, a user or a group, Click menu 【Policies > Show All Policies】 to see what policies are applied to selected object. Click the Expand or Collapse button ![]() to view or hide all policies.
to view or hide all policies.
| System Event Logs | Back to Index | Basic Policy |