AnySecura can be used as centralized computer maintenance system to manage and control software and hardware assets. Besides, device control policy is available to forbid the usage of the unwanted devices.
Good computer maintenance habits can keep your computer away from trouble and enable you to use them under a perfect performance. Computer maintenance sounds like a complicated issue since both hardware and software problems are involved. As an employer, have you ever thought about hiring a professional for computer maintenance? Actually, you don't need to. With AnySecura, maintaining computers is as easy as falling off a log.
- Do you want to know what software they installed? What system services they enabled or disabled?
- Did they plug in USB device to copy files? Did they burn confidential documents to DVD?
AnySecura’s is a great assistant to help administrator and supervisor to maintain the computers. You can view their computer names, IP addresses, MAC and more, disable devices, check and manage their hardware and software assets, end processes or programs, stop system service and file sharing, check PC performance, check disk usage, remotely lock, shutdown, log off or restart the computers, remotely transfer files and set up remote control connections.
View the real-time PC status
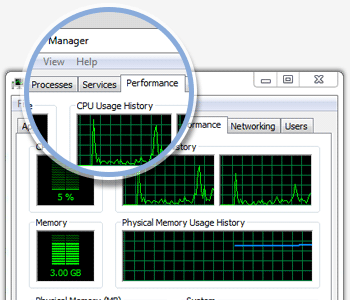
You can view real-time PC status, inicluding running applications, processes, PC performance, device manager, services, disk management, shared folders, scheduled tasks, users and groups, softwar e management, remote control and remote file transfer.
Manage the real-time PC status
In console, you can remotely close applications, end processes, disable or enable hardwares, start or stop services, stop sharing folders, stop scheduled tasks and uninstall software.
- Check the real-time information and running processes of remote computers. Display all running applications, end harmful or unexpected application or any selected application
- Display process list with file name, PID, time, section ID, CPU usage, CPU time, memory usage, virtual memory uages, priority, handle, thread count and file path, end process if necessary
- Show computer performance status including total CPU usage, total memory usage, sum of handle, thread count, and processes, physical memory, commit and kernal memory
- Enable or disable any device with remote device manager
- List all system services with service description, status, startup type, log on as and service path. Start or stop any service
- Check disk status with volume name, file system, capacity, free space and percentage of used space
- List all shared folders with folder name, folder path and numbers of agent connection, stop file sharing
- List all scheduled tasks with task name, schedule time, task path, next run time, last run time, status, last result and creator. Delete any unwanted scheduled task
- Display users and groups of computer management with full name and description
Check Basic Info & Basic Event
- Record all computers basic information including Name, Computer Name, IP address, installed agent version, OS version, last online time, last active time, agent's installed time and last logon user
- Record computers' basic events including logon, logoff, startup and shutdown with time
Check Software & Hardware Assets
- Check asset change for both software and hardware
- Record operation types including Add, Delete, Change modes
- Record operation type, operation time, user group, user name, asset type and description
- Provide convenient assets change search filters
Device Control Policy
- Block or enable Storage Device including floppy, CDROM, burning device, tape and removable storage device
- Block or enable Communication Interface Device including COM, LPT, USB controller, SCSI controller, 1394 controller, infrared, PCMCIA, bluetooth, modem, directly lines and Dial-up connection
- Block or enable USB Device including USB keyboard, USB mouse, USB modem, USB image device, USB CDROM, USB storage, USB harddisk, USB LAN adpator and other USB devices
- Block or enable Network Devices including wireless LAN adapter, PnP adapter and Virtual LAN adapter
- Block or enable audio equipments, virtual CDROM and any other new devices
Policy Example
Employers want to prevent copying or burning any files.
Device Policy Property Settings:
1. first set a policy by choosing "block" mode.
2. click ... button on the right of device policy, choose all storage devices and USB CDROM, USB storage and USB HardDisk under USB device list.
If you only want to protect some confidential files, you can use Document Policy instead.