SurveilStar invisible computer monitoring software runs in total stealth mode that will secretly record and monitor live desktop activities including website visits, application usage, instant chat messages, incoming and outgoing emails, document operations, print actions, network access, device usage, and etc.
Want to secretly monitor your employee, spouse or children computer activities? SurveilStar is the most reliable computer/internet monitoring software available. SurveilStar Agent is completely invisible. No trace of our monitoring software appears in the Registry, the Process List, the System Tray, the Task Manager, on the Desktop, or in Add/Remove Programs. There aren't even visible files that can be seen!
SurveilStar isn't disrupted by any known firewall software and hardware - so it runs without raising any red flags. Even many popular anti-monitoring and anti-virus software applications currently available can't see that SurveilStar Agent is running!
SurveilStar offers industrial grade invisibility combined with the ability of remote monitoring (meaning you don't have to physically access the computer you're monitoring in order to view what's been recorded) to guarantee that you can keep an eye on things without interfering with day-to-day computer activities.
Whether you need to monitor an employee, a family member, or anyone else, you'll be using the latest in invisibility technology with SurveilStar computer monitoring software.
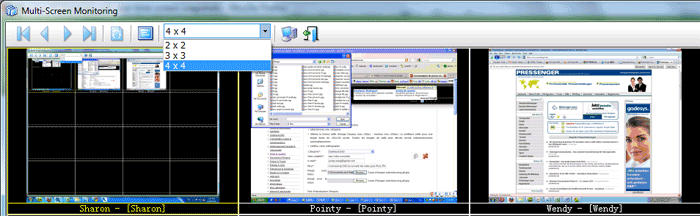
SurveilStar enables you to monitor your employees’ on-screen activities and know what they do with their computers in a completely invisible mode. Moreover, it also provides multi-screen viewing and screen history viewing functions. With the multi-screen monitoring function, you can monitor several employees at one time. By viewing screen history, you can easily obtain pure and impartial proof of any illegal operations.
In addition, screen history can be exported to video and played by Windows Media Player for your review in the future. Screen monitoring is the most powerful way to visually record and review everything your employees do online and offline.
SurveilStar runs completely invisibly allowing you to control the emails sending out of your corporation. It enables you to easily control outgoing emails by specifying sender, recipients, email subject, file name, type and size of attachment.
SurveilStar supports invisibly recording webmail (e.g., hotmail, Yahoo! Mail), SMTP/POP3 email, Exchange and Lotus email. Administrator can make different policies to control all outgoing emails by specifying sender, recipient, email subject, has or do not have attachment, and how big the size of attachment are allowed to be sent out of the company.
SurveilStar enables you to secretly monitor IM activity, and record instant message history of agent computers. SurveilStar lets you know what your employees are doing using IM applications, how long do they spend on personal chatting during office hours and how often do they chat.
SurveilStar lets you monitor MSN, ICQ, YAHOO! Messenger, Skype, Lotus Sametime, SINA UC, QQ, TM, RTX, POPO, LSC, ALI, FETION, Google Talk, etc. without being noticed.
SurveilStar is completely invisible to computer users, allowing administrators stealthily control and monitor employees’ web browsing behavior, know every web site they visit and what they do on each web site.
Based on collected detailed log, web statistics and complete analysis report, system administrators can have a better understanding of users’ web browsing behavior. Such data could also be used as a reference for policy planning and management purposes; for instance, as an indication of which websites to be blocked or limited in order to increase work efficiency.
SurveilStar offers superior invisible application monitoring. It gives administrators the power to monitor application usage, and know what the employees type into those applications, such as in word processors, spreadsheets, databases, presentations, games, etc.
SurveilStar also provides administrators with detailed logs, application statistics and complete analysis reports which can assist them in understanding user behavior. Moreover, it is useful for management purpose. For example, its statistics will serve as a reference for answering issues like what applications should be controlled in order to increase work efficiency.
Running in secret invisible mode, SurveilStar provides ways to control and monitor all documents operated in different types of storage media, including local hard disk, network drives, CDROM, floppy drive and removable disks.
IT administrator can set different policies targeting on different types of disks to control the file operations such as read, modify and delete; the typical examples are to protect important files which cannot be deleted; to limit different users to access specified network shared drives; to prohibit user from playing MP3 files; all removable disks only have read-only access right and so on. All these policies can be applied to specified groups or users.
With SurveilStar invisible printing monitoring function, administrator is able to control agent computers' access to different types of printers including local, shared, network and virtual printers.
Also, if Record Printed Image is optionally selected, all backup printed files are saved into image formats. Moreover, the detailed print log includes printer type, time, computer name, user name, print task, printer name, number of printed pages, document caption and application by which the file was printed.
SurveilStar's invisible network monitoring feature allows administrators to effectively stop illegal computers from accessing computers within the internal network to prevent information leakage.
By controlling network ports, administrators can block malicious ports and download ports in order to keep away from virus and protect internal network security. Moreover, administrator can reasonably control the access rights of different apartments so as to standardize company management.
SurveilStar provides ease of logging operations of each agent computer, executing policies and monitoring. One of the modules in IP-guard called Device Management facilitates IT administrators to manage endpoint devices including storages, communication devices, dial services, USB devices, network devices and other devices such as audio and virtual CDROM, etc.
What IT administrators have to do is to set control policies for specified devices and the policies will be automatically distributed to the agent computer immediately and then executed instantly. All triggered events are logged and IT administrators can trace the details through the console easily.